The system is touted as being healthcare, but in reality it is being used as an illegal surveillance which takes away the individuality, the privacy, the dignity and independence of a human being. Every activity is recorded. Someone watches every activity, including bathroom activities and having sex. Every heartbeat and breath can be monitored and recorded. Note that they can communicate using satellites and drones.
What is Biotelemetry?
Biotelemetry (or medical telemetry) involves the application of telemetry in biology, medicine, and other health care to remotely monitor various vital signs of ambulatory patients. Virtually any physiological signal could be transmitted.
A typical biotelemetry system is comprised of (1) sensors appropriate for the particular signals to be monitored, (2) a battery but some do not require batteries because they are stimulated with frequency or light (3) a radio antenna and receiver, and (4) a display unit or monitor to display information from patients.
Click On Pic To Enlarge
A Very Low Power MAC (VLPM) Protocol for Wireless Body Area Networks
by Niamat Ullah *, Pervez Khan and Kyung Sup Kwak
Published: 25 March 2011
Abstract: Wireless Body Area Networks (WBANs) consist of a limited number of battery operated nodes that are used to monitor the vital signs of a patient over long periods of time without restricting the patient’s movements. They are an easy and fast way to diagnose the patient’s status and to consult the doctor. Device as well as network lifetime are among the most important factors in a WBAN. Prolonging the lifetime of the WBAN strongly depends on controlling the energy consumption of sensor nodes. To achieve energy efficiency, low duty cycle MAC protocols are used, but for medical applications, especially in the case of pacemakers where data have time-limited relevance, these protocols increase latency which is highly undesirable and leads to system instability. In this paper, we propose a low power MAC protocol (VLPM) based on existing wakeup radio approaches which reduce energy consumption as well as improving the response time of a node. We categorize the traffic into uplink and downlink traffic. The nodes are equipped with both a low power wake-up transmitter and receiver. The low power wake-up receiver monitors the activity on channel all the time with a very low power and keeps the MCU (Micro Controller Unit) along with main radio in sleep mode. When a node [BN or BNC (BAN Coordinator)] wants to communicate with another node, it uses the low-power radio to send a wakeup packet, which will prompt the receiver to power up its primary radio to listen for the message that follows shortly. The wake-up packet contains the desired node’s ID along with some other information to let the targeted node to wake-up and take part in communication and let all other nodes to go to sleep mode quickly. The VLPM protocol is proposed for applications having low traffic conditions. For high traffic rates, optimization is needed. Analytical results show that the proposed protocol outperforms both synchronized and unsynchronized MAC protocols like T-MAC, SCP-MAC, B-MAC and X-MAC in terms of energy consumption and response time.
by Enrique Gonzalez, Published: 22 May 2015
Abstract: This survey aims to encourage the multidisciplinary communities to join forces for innovation in the mobile health monitoring area. Specifically, multidisciplinary innovations in medical emergency scenarios can have a significant impact on the effectiveness and quality of the procedures and practices in the delivery of medical care. Wireless body sensor networks (WBSNs) are a promising technology capable of improving the existing practices in condition assessment and care delivery for a patient in a medical emergency. This technology can also facilitate the early interventions of a specialist physician during the pre-hospital period. WBSNs make possible these early interventions by establishing remote communication links with video/audio support and by providing medical information such as vital signs, electrocardiograms, etc. in real time. This survey focuses on relevant issues needed to understand how to setup a WBSN for medical emergencies. These issues are: monitoring vital signs and video transmission, energy efficient protocols, scheduling, optimization and energy consumption on a WBSN.
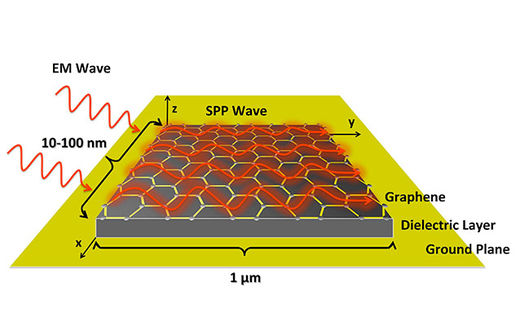
Click On Pic To Enlarge
The challenge of designing in-body communications
https://www.embedded.com/the-challenge-of-designing-in-body-communications/
The range of medical devices and systems being implanted into the human body is increasing rapidly. Evolving from the first implanted pacemaker in the late 1950s, today's in-body devices are now being used to regulate bodily functions, stimulate nerves, and treat diseases such as Parkinson's, Alzheimer's, and epilepsy.
Figure 1: Almost every aspect of a patient's health can now be monitored or regulated by an implanted device.
As Figure 1 shows, almost every aspect of a patient's health can now be monitored or regulated by an implanted device. These range of devices pose unique power, signal processing, and communication challenges for designers.
The 402- to 405-MHz band is well suited for in-body communications networks, due to signal propagation characteristics in the human body, compatibility with the incumbent users of the band (meteorological aids, such as weather balloons), and its international availability. The MICS standard allows 10 channels of 300kHz each and limits the output power to 25μW.
Medical devices can be categorized into those that use an internal non-rechargeable battery (such as pacemakers) and those that couple power inductively (such as cochlear implants). The former employs a duty-cycling operating system to conserve power. The transceiver is “off” most of the time, meaning the off-state current and the current required to periodically look for a communicating device must be extremely low (less than 1μA).
Sensors (Basel). 2011; 11(6): 5561–5595.
Published online 2011 May 26. doi: 10.3390/s110605561
PMCID: PMC3231450
PMID: 22163914
Wearable and Implantable Wireless Sensor
Network Solutions for Healthcare Monitoring
Ashraf Darwish1,* and Aboul Ella Hassanien2
Author information Article notes Copyright and License information Disclaimer
This article has been corrected. See Sensors (Basel). 2012; 12(9): 12375.
Abstract: Wireless sensor network (WSN) technologies are considered one of the key research areas in computer science and the healthcare application industries for improving the quality of life. The purpose of this paper is to provide a snapshot of current developments and future direction of research on wearable and implantable body area network systems for continuous monitoring of patients. This paper explains the important role of body sensor networks in medicine to minimize the need for caregivers and help the chronically ill and elderly people live an independent life, besides providing people with quality care. The paper provides several examples of state of the art technology together with the design considerations like unobtrusiveness, scalability, energy efficiency, security and also provides a comprehensive analysis of the various benefits and drawbacks of these systems.
IMPLANTS FOR MEDICAL USE AND FOR TORTURE
Above and below, you will see diagrams of a person who has been implanted with medical devices in what is called a Wireless Body Area Network (BAN). Implants are sensors that are connected with computers by means of a cell phone which communicates to medical, law enforcement and Homeland Security. Also sensors in humans can be connected to implants in other humans and to the sensors in homes, furniture, vehicles, buildings, electrical wiring, roads, etc.
The implants in a BAN are very similar to a diagram of a person called a Targeted Individual who has been implanted with medical devices for the purposes of tracking, stalking, harassing, surveilling, torturing and killing them. They are tortured in their home, vehicle and public places outside and inside. This indicates that the infrastructure in the Smart Grid is being used against them instead of for medical purposes. Organized stalking is carried on by contractors, including police, firemen, medical EVAC personnel, veterans and others. See COPS program. Smart phones are being used to stimulate the implants in TI's.